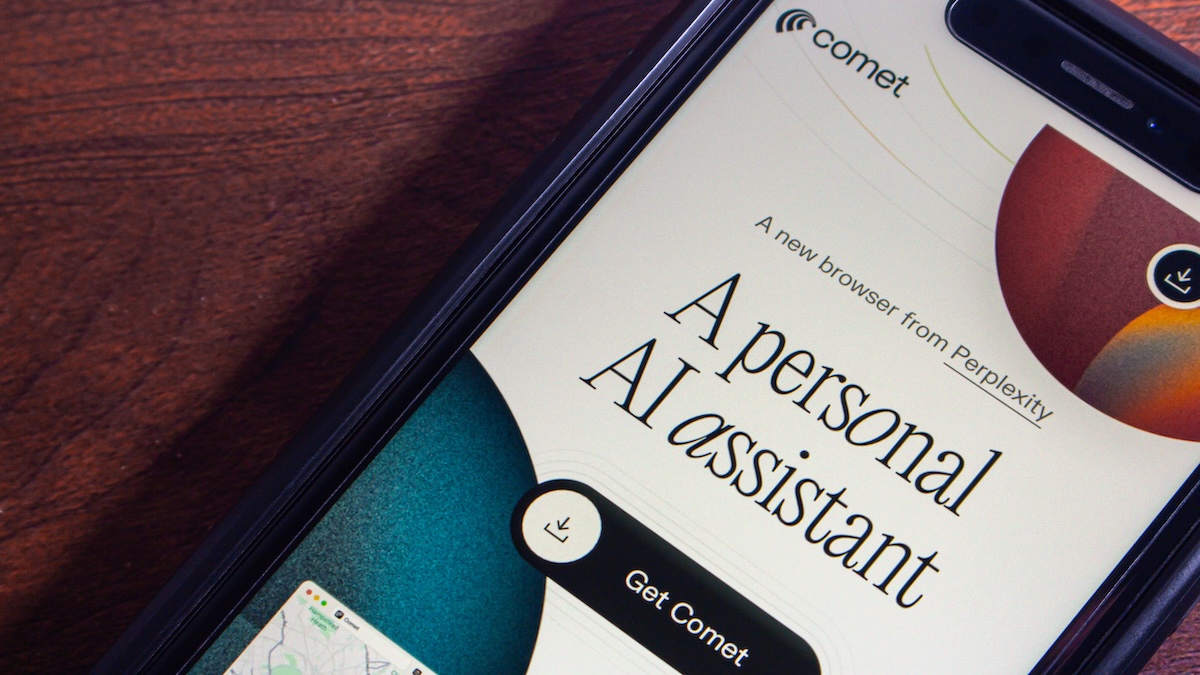
Shortly after AI search engine company Perplexity launched its Comet AI browser, threat actors attempted to capitalize on it by luring users to fraudulent domains and fake applications, threat intelligence firm BforeAI reports.
Launched in July, Comet is a Chromium-based browser that integrates Perplexity’s AI assistant, offering support for automating tasks, organizing emails, and researching the web.
Beginning August, BforeAI observed an increase in fraudulent domains promoting an executable version of the browser available for download via third-party websites.
Analysis of over 40 suspicious domains showed the use of typo-squatting, brand impersonation, and deceptive advertisements to lure users to the fraudulent websites.
The threat actors behind this coordinated campaign used several keyword variations containing ‘comet’, ‘AI’, ‘browser’, ‘perplexity’, and ‘download’.
Eight of the domains were registered after Comet was launched, including cometai.site, cometaibrowser.com, perplexitycomet-ai.com, cometbrowser.net, and aicometbrowser.com, which are considered critical- and high-level threats.
The cometai.net domain, the threat intelligence firm notes, has been parked for $9,999 on GoDaddy.
Additionally, BforeAI identified two critical-level mobile application threats in the Google Play Store, such as Comet AI Atlas App Info, which directly impersonates the browser.
A fraudulent iOS application was also identified, and Perplexity CEO Aravind Srinivas warned of its existence earlier this month.
“The Comet app currently on iOS App Store is fake and spam and not from Perplexity,” his public warning reads.
The threat intelligence firm also discovered Google ads promoting fraudulent Comet downloads and social media ads that directed to fake sites, and linked them to the same campaign.
“The timing of domain registrations closely follows Comet’s launch timeline, indicating opportunistic cybercriminals monitoring for emerging technology trends. The use of international registrars, privacy protection services, and parking pages suggests coordination among threat actors,” BforeAI notes.
Related: AI Sidebar Spoofing Puts ChatGPT Atlas, Perplexity Comet and Other Browsers at Risk
Related: Browser Extensions Pose Serious Threat to Gen-AI Tools Handling Sensitive Data
Related: Browser Security Under Siege: The Alarming Rise of AI-Powered Phishing
Related: The Shadow AI Surge: Study Finds 50% of Workers Use Unapproved AI Tools